We asked Kjell Kjebekk, Head of Business Security for Telenor in Norway, about the cybersecurity challenges and threats on the rise in companies today.
In our discussion, Kjell reveals critical cybersecurity solutions, detailing what enterprise organizations can do to protect themselves.
Here’s what Kjell shared:
What is the most challenging security issue(s) facing enterprises currently?
Kjell: Our new geopolitical reality requires us to think differently to protect societal values. Those who attack us actively work daily to discover the weak links in Norway's digital infrastructure.
They are less concerned about whether they attack private companies, municipalities, hospitals, or the military infrastructure. At the same time, and regardless of the geopolitical situation, the threat posed by organized cybercrime is ever-increasing.
Financially motivated and organized cybercriminals operate opportunistically, for example, when ransomware attacks that exploit known vulnerabilities hit vulnerable businesses, regardless of who they are, for the most part.
The police say in their threat assessment for 2022 that data breaches and ransomware are crime phenomena that could affect all Norwegian public and private businesses in the years to come.
Do you see an evolution happening in the corporate mindset toward cybersecurity challenges?
Kjell: In recent years, several Norwegian institutions, agencies, companies, municipalities, and media houses have been exposed to extensive cyber-attacks that have majorly impacted their ability to deliver goods and services, and some have even threatened state security.
Several of these attacks have received considerable media attention. It is positive that there is more transparency about these attacks and what methods the attackers use.
Companies previously wanted as little attention as possible. They were afraid to expose their mistakes and weaknesses publicly. Still, now we see that more people are open about their experiences. This kind of knowledge sharing makes us all better equipped.
What does cybersecurity have to do with corporate culture?
Kjell: Occasionally, there is talk about the "security culture" in companies as if it is a separate issue. But companies that succeed in security in a way that corresponds to the real threat picture and the desired level of risk in the business are the ones that manage to establish security as part of the corporate culture in everything they do.
Good IT security is a combination of stable and secure architecture, along with an organization that keeps the systems secure and up to date – and can detect if damage has occurred and has good processes across the organization to close these incidents.
It is a challenge of knowledge and competence for managers, technologists, and other employees who face daily choices and must take actions that could have consequences for cybersecurity.
What's the most important thing companies should consider when working with IT vendors or other technology providers regarding security?
Kjell: Most companies have digitalization high on their agendas, while security has been further down. Security in supply chains is critical.
It is about setting requirements for suppliers and ensuring that these requirements are passed on to subcontractors – implementing security and control mechanisms for suppliers and deliveries, requiring strong expertise for most businesses.
Security in supplier/supply chains is not only about what comes from subcontractors but also about one's role in supply chains. It is essential to consider that you, as a supplier, bear the risk for your customers.
What are the three most important steps that organizations can take when it comes to cybersecurity solutions?
Kjell:
- Systematically add the basics. There are many well-known best practice frameworks and guidelines to choose from. The company's maturity, industry affiliation, and operational jurisdiction should influence the choice. Many governments issue clear policies on which basic measures to prioritize if the current maturity of cybersecurity in the enterprise is moderate to low. The NSM (National Security Authority) Basic Principles are a good starting point in Norway.
- Start at the top. Senior executives must set a clear ambition for the organization's stance on cybersecurity, with a clear policy that is well communicated, along with a mandate and explanation on why this is important to the organization. If this is not anchored at the top, practical implementation will have little chance of success.
- Find competent partners: the type of expertise you need and the extent to which you need partners will vary, especially considering the organization's size. However, even large enterprises with capable cybersecurity teams will need niche expertise and additional resources through a partner who specializes in cybersecurity.
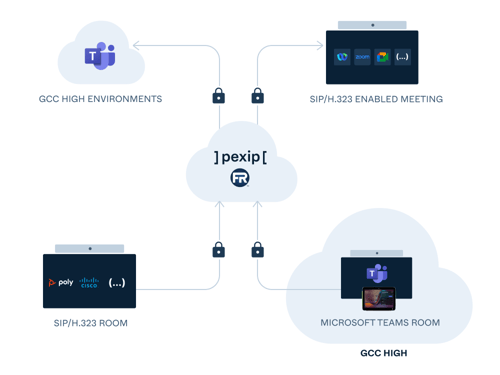
Find out how Pexip's secure video technology platform secures global organizations to help safeguard them against cybersecurity threats and breaches.
- Enterprise
- Meet & collaborate securely
- Business Continuity