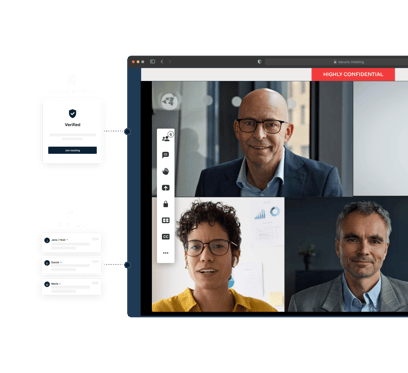
Zero trust–ready video meetings
Protect your most sensitive conversations with video conferencing built for strict zero-trust architectures
Applying zero trust to video collaboration
Traditional zero trust architectures focus on applications and data stores. Video collaboration introduces a dynamic layer of users, devices, and shared content that needs governing with the same rigor.
Pexip treats every meeting as a controlled data environment, which enables:
- Continuous verification of participants and sessions
- Just-in-time, just-enough access to meeting features and content
- Secure collaboration with internal and external users
- Elimination of static controls like PINs and shared links

Meetings under your control
Pexip’s open architecture make it possible to realize the potential of a fully-developed zero trust and data-centric environment.
Role and attribute-based access controls
Enforce RBAC and ABAC policies per participant through integration with your external policy engine. Access to meetings, breakout rooms, and content is granted dynamically — based on role, attributes, and context.
Learn how to restrict access with policiesMicrosegmentation of meeting data flows
Meeting traffic is isolated so a compromised user or device is prevented from moving laterally across other sessions or systems, containing threats and reducing lateral attack surface.
Read more about limiting threatsIdentity-based authentication
Integrate with your identity provider to extend SSO, MFA, and federated authentication directly into the meeting environment — aligned with your zero trust framework.
Read our access control ebookIntegrating video collaboration into a zero trust framework
Read more about zero trust
Secure video collaboration
Choose self-hosted video conferencing and ensure full regulatory compliance with robust protection standards tailored for every industry.